IBM i Security Access Controls MFA 2FA SIEM SYSLOG Big Data Encryption Compliance
IBM i security software for iSeries and AS400 systems including Exit Programs for network security access controls and auditing of user access, Profile Swapping for Privileged Access Management PAM, Multi-Factor Authentication MFA, secure Password Self-Service PSS, Encryption for DB2 and IFS Files, Masking and Scrambling for DB2 Database, File Integrity Monitoring FIM, OS400 Firewall for controlling IP Addresses and Ports, native sFTP client for Secure File Transfer, automated Security Audit Reporting with hundreds of predefined report templates, SIEM and SYSLOG Server integration, Job Scheduler, High Availability HA, Disaster Recovery DR, and other many other iSeries tools for compliance, IT and Help Desk services.
All IBM i security software includes free installation, implementation assistance and unlimited training for as long as the software has an active subscription or maintenance and support. Ask to do a trial of any software, and ensure our software meets all your requirements.
IBM i Encryption Masking and Scrambling
IBM i Authority Manager Auditor and Screen Capture
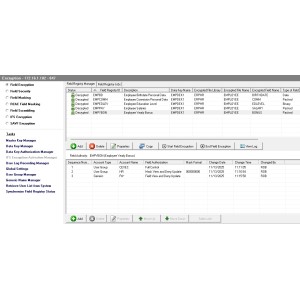
AS400 Firewall Manager
A native AS400 Firewall, providing granular network security controls and auditing for inbound and outbound TCP/IP traffic.
IBM i Security Suite
Enforcive Enterprise Security software for IBM i security and compliance requirements, includes exit point access controls, alerts and simplified auditing and reporting tools for system, network, SQL and DB2 database changes.
IBM i AES Encryption
IBM i AES encryption protects sensitive and private data at rest, no matter where it ends up or how it is accessed.
IBM i Multi Factor Authentication Solution (MFA)
IBM i MFA is a Multi-Factor Authentication compliance solution that prevents unauthorized user access to iSeries AS400 systems by adding additional single step authentication requirements.
IBM AS400 SFTP FTPS Secure FTP Manager
IBM AS400 SFTP FTPS Secure FTP Manager for iSeires provides secure FTP Client and Server functions, encrypts file transfer connection file contents in transit, supports sending and receiving from any platform and automates entire process.
iSeries MFA Solution for IBM i Multi Factor Authentication
IBM iSeries MFA for AS400 multi-factor authentication is a simple solution for securing 5250 sign-on, third party applications, web services and use case specific scenarios such as processes requiring elevated authority.
IBM i Event Log Forwarding for QRadar SIEM
iSeries QRadar SIEM enables collection and forwarding of IBM i AS400 event logs to QRadar SIEM in a normalized LEEF format with QID, log enrichment, and support any log source on system: QAUDJRN, Database Journals, QHST, Exit Points, Network Commands, SQL Statements, Open Source Protocols, Ports, Sockets, Accounting Journal, Collection Services, Spool Files, static data and other data sources.
iSeries SFTP Manager AS400
iSeries SFTP Manager for AS400 provides secure FTP Client and Server functions, encrypts file transfer connection via SSL and file contents in transit, supports sending to and receiving transfers from platform.
Tokenization for iSeries AS400
Tokenization for IBM iSeries AS400 can help eliminate regulatory compliance exposures by replacing sensitive data with a token that has no real value.
iSeries Profile Swapping Elevated Authority
Automatically elevate authority for powerful profile swapping and adopted authority policies using flexible automated rules for user group profiles, supplemental groups, lists of users and command line access requirements.
SFTP Manager for iSeries AS400
SFTP Manager for iSeries AS400 provides both secure FTP Client and Server functions, encrypts file transfer connection via SSL and files in transit, can send and receive transfers from any other platform.
iSeries 2FA for AS400 Two Factor Authentication
iSeries 2FA for AS400 two factor authentication is a simple solution for securing 5250 sign-on, third party applications, web services and use case specific scenarios such as processes requiring elevated authority.
AS400 Encryption for DB2 Database
AS400 encryption, masking and scrambling software provides a point and click GUI interface to implement IBM's native FIELDPROC exit program in minutes to protect iSeries AS400 DB2 database fields, rows and columns.
- 1
- 2