Is your SIEM the magic bullet? Many companies are finding their SIEM implementations have provided little return on investment and have not strengthened their security posture to any great degree. Purchasing the best SIEM and endpoint security tools on the market will not magically identify vulnerabilities, make an infrastructure more secure. Every SIEM requires proper implementation and ongoing tuning services to keep up with the constant changing landscape of threats, vulnerabilities and a customer’s own environment. Like any security product, every SIEM requires an experienced technician to configure it correctly, and enough staff must be trained to keep up with the volume of threats and alerts. The number of false positives and lack of discernable actionable alerts (false positives) a SIEM produces, is a direct result of the implementation, alert maintenance and tuning.
Security threats are escalating in sophistication, volume and severity at a rate most companies cannot keep up with. Millions of new threats are discovered each day and requires a dedicated security team to monitor and manage. An experienced Managed SIEM Service or SOC team knows to keep a log of all these security events from threat intelligence feeds, so rules can trigger accurate alerts based on current and past content. Threat intelligence feeds provide the security intelligence, data enrichment and logic needed to maintain a healthy SOC. A Managed SIEM that does not utilize fresh threat intelligence feeds for security AI, may as well not exist.
Like therapy, the first step is to be honest with yourself. Is your SIEM delivering the results you were promised, and with the efficiency seen during your sales demonstration? Are SIEM operators keeping up with all the alerts? If you answered “no”, your company should consider hiring qualified security experts to go over your SIEM setup and deployed rules. It is probably wise advice not to consider using the same individuals that originally implemented your SIEM or those responsible for the ongoing maintenance and health of your SIEM. If your SIEM has failed, it only makes sense to use a fresh group of eyes and possibly look at a fully Managed SIEM.
The good news is, your SIEM investment is not wasted, it only needs some loving care by security professionals proficient on your SIEM, installed security products and a good knowledge of existent threats. Personnel with solid security expertise is a heavily sought after commodity, and are worth their weight in gold to most companies. A good security analyst is becoming harder and harder to find, and the demand for their skillsets are climbing every day. Some companies are investing in employee training to manage their SIEM, which is an excellent practice every company should be doing. Security and SIEM security training is a must, regardless of how big or small a company’s SOC is. Contact us if you have employees that need security or SIEM training. We have trained security analysts and engineers that can provide your SOC team with the necessary training they need to strengthen your company’s security posture.
Most companies do not want to be security experts, and simply want to focus on their core reason for being in business. Others are finding it difficult to attract qualified security analysts or find it too costly to manage their SIEM properly. If your company falls into these categories, your company should consider using a Managed SIEM as a Service, in which the SIEM can be on your premises or in the Cloud. If your company is small enough (has a low volume of events per minute ingested by the SIEM), your company can use a Hosted SIEM provider. Contact us with your Managed SIEM and Hosted SIEM requirements for a SOW, quote or to schedule a demonstration. Our security teams are proficient in managing QRadar, Splunk, AlienVault, and Exabeam SIEMs.
Our managed SIEM (SIEMaaS) offerings include monitoring and analyzing security events and alerts, to provide accurate actionable security intelligence and recommend necessary remediation steps. SOC security engineers will assess alerts, validate and add relevant security intelligence and facts to incidents before alerting customer contacts. If desired and contracted, our SOC security engineers can investigate every potential threat, malicious activity and vulnerability, and apply updated logic and intelligence for your SIEM to eliminate future time spent on false positives. Once real threats are discovered, SOC engineers can take agreed to actions by remediating the threats from targeted systems or deliver remediating recommendations to customer to respond and perform on thier own. Every SIEMaaS engagement is tailored to support and assist the customer based on their needs. Every company will have customized threat severity levels, processes, and escalation procedures based on their environment and corporate hierarchy.
If your company wants to be completely out of the security business, and hands off monitoring, security incidents, response and technical changes for your entire IT infrastructure, we can provide these services also. Security as a service (SECaaS) or Security Operations Center as a Service (SOCaaS) are security management outsourcing offerings for companies that realize somethings are better left to the professionals. SECaaS and SOCaaS are becoming very popular these days due to many reasons. These managed security services can be all encompassing managed security engagements or tailored to offset specific areas your company has deficiencies. SECaaS and SOCaaS offerings can also be provided when your company simply needs more hands on deck for one off incidents, deep forensic analysis, ad-hoc changes in response to an incident, implementation of new security technology and network architecture consulting and build-outs.
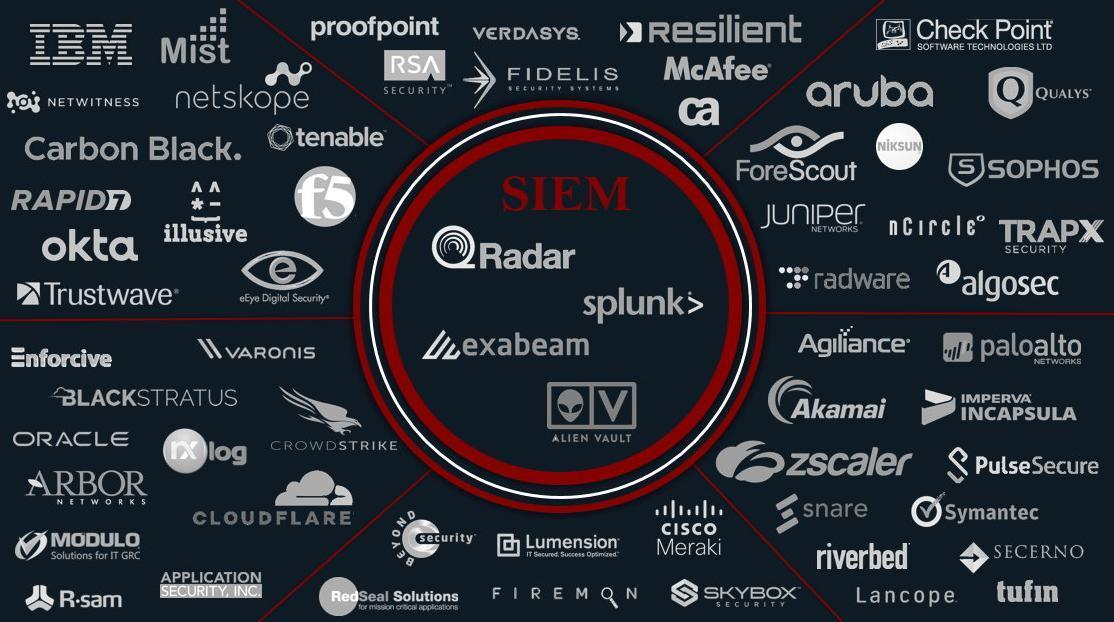
We can provide all or any of these managed security roles. We support and provide services for the most commonly used and best of breed security products on the market. Below is a list of some of the technology vendors you may need help with:
SOC and Security Information Event Management (threat intelligence): QRadar, Splunk, Exabeam and AlienVault
Endpoint Protection: Carbon Black, Palo Alto, Check Point, Sophos, CrowdStrike, McAfee and Symantec
Network and Firewall: Cisco, Check Point, Fortinet, Juniper, Palo Alto and HP Aruba
Web Application Firewall: zScaler, f5, CloudFlare and Palo Alto
Cloud Application and Email Security: NetSkope, zScaler, Palo Alto and Proof Point
Identity and Access Management: Okta, ForeScout, Pulse Secure and HP Aruba
Vulnerability Scanning: Rapid7, Qualys, IBM and Alien Vault
DDoS Mitigation: Incapsula, Akamai, CloudFlare, RadWare, Arbor and Corero
DNS Security: Palo Alto, CloudFlare and zScaler
File Integrity Monitoring: NXLog, Snare and Varonis
Wireless Access Points: Cisco, Meraki, HP Aruba and Juniper Mist
Attacker Deception: TrapX Security and Illusive
Industrial Control Systems and Operational Technology: Palo Alto and ForeScout
Our experienced security teams monitor and manage customer environments 24/7 in over 30 different countries, helping businesses of all sizes decrease risk and operation expenses. Our security specialist teams are located in the US and UK, and providing unparalleled access to real-time threat reports, breach prevention and general network security services.